In January, I was invited by Flatiron School London to give a talk on how I switched careers from Business consulting to the Tech industry.
They’ve also interviewed me on how to become a Security Engineer. I wanted to share it with everyone :-)

When did you first start coding?
My first experience with computers and programming was with a Sakhr AX-170 MSX in the mid 80s when I was in Saudi Arabia. It was really raw as there was no feedback from the machine and it would require me to go through dry computer books to learn more. The language was BASIC. This was also my first experience with video games and Konami games.
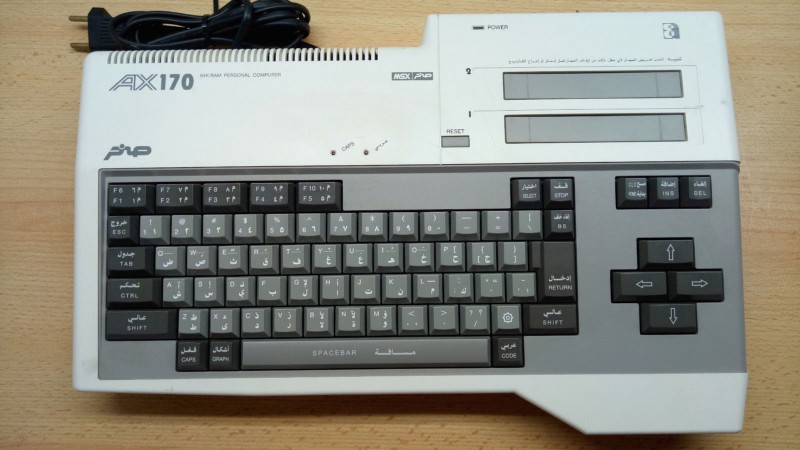 _[Sakhr AX-170 — MSX Wiki](https://www.msx.org/wiki/Sakhr_AX-170" rel="noopener" target="blank" title=")
_[Sakhr AX-170 — MSX Wiki](https://www.msx.org/wiki/Sakhr_AX-170" rel="noopener" target="blank" title=")
After that I continued to dabble with coding and different programming languages such as XHTML, CSS, HTML 4.0, ECMASCRIPT 3 and PHP (MAMP tech stack). I was creating simple static websites on video games or playing with the CSS on MySpace.com.
What qualifications do you need to get into security?
It all depends on which branch of Cyber Security you want to work in. Some people have a Computer Science degree or certifications, and others are self taught.
There are several well-recognised and respected certifications for security professionals from organisations like (ISC)², ISACA or the SANS Institute.
Cybersecurity and IT Security Certifications and Training | (ISC)²
_Prove you're a leader in your field with our globally recognized cybersecurity certifications. Help make the cyber…_www.isc2.org
Information Technology - Information Security - Information Assurance | ISACA
_ISACA® is a nonprofit, independent association that advocates for professionals involved in information security…_www.isaca.org
Information Security Training | SANS Cyber Security Certifications & Research
_SANS Institute is the most trusted resource for information security training, cyber security certifications and…_www.sans.org
The CompTIA is another great organisation where you can learn more about IT fundamentals, networks, cloud, linux, servers and security with different tracks for each profile.
CompTIA Security+ Certification
_CompTIA Security+ sets the standard for best practices in IT security and risk management._certification.comptia.org
You can find some good MOOCs on Udacity, Coursera or edX.
Introduction to Cybersecurity | Udacity
_Explore the fundamental building blocks of cybersecurity._eu.udacity.com
If you are more interested in penetration testing, the Offensive Security Certified Professional would be a great certification to have.
Offensive Security Certified Professional
_Offensive Security Certified Professional (OSCP) is the certification for Penetration Testing with Kali Linux, the…_www.offensive-security.com
You can also become the Security Champion of your team. This is what I did in my company. You can start in the development team and act as the Security Champion.
Security Champions Playbook - OWASP
_According to OWASP definition, Security Champions are "active members of a team that may help to make decisions about…_www.owasp.org
You will be an active member of the team and may help make decisions about when to engage with the Security Team. You’ll act as the voice of security for a given product, feature or team, and assist in the triage of security bugs.
You can help implement an AppSec pipeline, raise tickets on JIRA and write some documentation on the Wiki or Confluence. You can collaborate within the network of Security Champions, attend meetings, be the go-to person, ensure security is not a blocker, get some training and help with QA and testing.
Once you have the experience and if you’re interested in the industry, you can engage with your Security Team and try to make the move within your company, then get more experience and certifications as you go.
Are there any resources you would recommend?
A good start for the developers would be the Open Web Application Security Project (OWASP) where they will find everything related to software security.
 _OWASP website. [https://www.owasp.org/index.php/Main_Page](https://www.owasp.org/index.php/Main_Page" rel="noopener" target="blank" title=")
_OWASP website. [https://www.owasp.org/index.php/Main_Page](https://www.owasp.org/index.php/Main_Page" rel="noopener" target="blank" title=")
Usually developers might be familiar with the OWASP Top 10 Most Critical Web Application Security Risks, which is a good start
Category:OWASP Top Ten Project - OWASP
_The OWASP Top 10 is a powerful awareness document for web application security. It represents a broad consensus about…_www.owasp.org
It is worth having a look at other projects like the OWASP Top Ten Proactive Controls, which is a list of security techniques that should be included in every software development project. There’s also the OWASP Application Security Verification Standard (ASVS) Project, which provides a basis for testing web application technical security controls and also provides developers with a list of requirements for secure development.
OWASP Proactive Controls - OWASP
_The OWASP Top Ten Proactive Controls 2018 is a list of security techniques that should be included in every software…_www.owasp.org
OWASP Application Security Verification Standard Project - OWASP
_The primary aim of the OWASP Application Security Verification Standard (ASVS) Project is to normalize the range in the…_www.owasp.org
You can join their local meetup in your city or their slack channel, and everyone is free to participate in their project. This could be a good starting point in contributing to an open source project and a great item to have on your CV and GitHub profile.
OWASP London
_OWASP (The Open Web Application Security Project) is a worldwide not-for-profit organisation focused on improving the…_www.meetup.com
I would also recommend to install Virtual Box and spin up a Kali Linux Box to get familiar with the suite of tools that professionals are using.
Our Most Advanced Penetration Testing Distribution, Ever.
_Home of Kali Linux, an Advanced Penetration Testing Linux distribution used for Penetration Testing, Ethical Hacking…_www.kali.org
You can then practice your hacking skills legally on some websites, CTFs (Capture The Flag) and Wargames like hackthebox, pwnable.kr, OWASP Webgoat, or the OWASP Juice Shop Project.
There are a lot of websites and CTFs available to practice. Don’t be afraid to try and fail, you will learn a lot through the process.
Hack The Box :: Penetration Testing Labs
_An online platform to test and advance your skills in penetration testing and cyber security. Join today and start…_www.hackthebox.eu
OWASP Juice Shop Project - OWASP
_Pwning OWASP Juice Shop is the official companion guide for this project. It will give you a complete overview of the…_www.owasp.org
If your company has a training budget, you could try to get a subscription for your team for platforms like Immersive Labs, Avatao or Secure Code Warrior to have hands on experience through online labs.
Cyber learning reimagined | Immersive Labs
_Immersive Labs is the world's most advanced cyber skills development platform. We are the cyber skill experts, helping…_immersivelabs.co.uk
Secure Code Warrior | Learn secure software development
_Secure your code from the start with gamified, scalable online security training for software developers._securecodewarrior.com
Finally you can register on crowdsourced cybersecurity platforms like BugCrowd or HackerOne where you will join a pool of security researchers, try to find bugs/vulnerabilities on commercial websites, and get paid for it. Depending on the company, you can get simple kudos or a sticker up to good monetary rewards if the vulnerability found is critical.
Bugcrowd | #1 Crowdsourced Cybersecurity Platform
_With a powerful platform and team of experts, Bugcrowd connects organizations to a global crowd of trusted security…_www.bugcrowd.com
Bug Bounty - Hacker Powered Security Testing | HackerOne
_HackerOne develops bug bounty solutions to help organizations reduce the risk of a security incident by working with…_www.hackerone.com
What advice would you give to our students?
Set goals and be really disciplined. There’s always something new to learn in this industry as it is constantly evolving and fast-paced. Companies need to address the cyber skills shortage, so there is a lot of demand.
The same tips for the Tech industry can apply to Cyber Security. Blogs are a great resource to learn more on application security, network security, threat modeling, incident/response, security operations center, red/blue/purple teaming, etc.
Follow the organisations and the people involved in this industry on Twitter. This is the best way to get the latest news, breaches, white papers, reports, events, conferences, meetups, etc.
YouTube has also great channels to follow (Troy Hunt, Security Weekly, LiveOverflow, HackerSploit, IppSec, IT Dojo, OWASP, DevSecCon, BugCrowd, HackerOne, AWS, etc.).
LiveOverflow
_just a wannabe hacker... -=[ ❤️ Support me ]=- Patreon per Video: https://www.patreon.com/join/liveoverflow YouTube…_www.youtube.com
HackerSploit
_About HackerSploit HackerSploit is a Cybersecurity training and consulting company that specializes in: Cybersecurity…_www.youtube.com
IppSec
_You probably know about my channel. Here's a bunch of other content I enjoy. Patreon Pages of Cool People…_www.youtube.com
IT Dojo
_IT Dojo is an IT Training and Consulting company that has a primary focus on cybersecurity, information assurance, and…_www.youtube.com
DevSecCon
_DevSecCon is a conference that features talks and workshops about DevSecOps - a new approach that thrives to embed…_www.youtube.com
Bugcrowd
_Learn more about security, testers, and the bug bounty through Bugcrowd's official YouTube Channel. Bugcrowd provides…_www.youtube.com
HackerOne
_HackerOne is the no.1 bug bounty and vulnerability disclosure platform, connecting organizations with the world's…_www.youtube.com
Join meetups where you can get more insights. OWASP and ISC2 have their own chapters. Ladies of London Hacking Society (LLHS) is a great meetup for women in cybersecurity.
LLHS Ladies of London Hacking Society
_An offensive & defensive technical security meetup for women.Women centric not women exclusive, Men who want to give a…_www.meetup.com
Look on websites like meetup.com or eventbrite.com. You can also attend some free cybersecurity events or conferences.
Don’t forget that security should be involved at every level, try to push left during the software development life cycle, don’t be afraid to engage with your security team in your company or the security community online.
And even if you don’t want to follow a career in cybersecurity, knowing a little bit more on that topic will make you a more well rounded software engineer.
What is the most important lesson life has taught you?
I have a motto which is stay curious, keep on hacking and make it happen. But the most important thing I’ve learned is that passion and grit are fundamental.
If you’re passionate about something, just do it, because it is worth it and don’t listen to what others would say. If some people tell you “no, this is silly, you can’t do it”, ignore them. You can do it if you put effort and time in it.
When I was in South Korea, I moved from being a Business Consultant to being a Software Engineer. The journey was not easy at all. I wanted to flip tables (and computers) too many times, but I was driven by challenges and, passion and grit kept me on track. I had a long term objective to reach.
Don’t forget to share your struggles — you would be surprised by the number of people going through the same feelings as you during this journey. And don’t let imposter syndrome get you down, everybody is having it at different levels. Be optimistic, confident and creative.
Also don’t forget to share your victories/achievements, small or big, it doesn’t matter. Celebrate them when you reach a milestone. It is important to keep you motivated.
Keep learning, keep meeting and sharing with people, and keep challenging yourselves!
More on my journey from Business to Tech :-)
Sonya’s journey: International business consultant to full-stack dev
_Welcome to Awesome Women in Tech, where we meet inspirational women making waves in the industry._medium.com
 #StayCurious, #KeepOnHacking and #MakeItHappen
#StayCurious, #KeepOnHacking and #MakeItHappen
If you have other resources, share them below in the comments!
You can also follow me on Medium, Twitter, Github and LinkedIn.

