You’ve probably heard of some of the large cyber-attacks like the Solarwinds hack that have happened recently.
Or maybe you've read about other futuristic attacks on power plants or water treatment plants that are modified remotely so as to take them offline.
As the world gets increasingly digitized, the risks and rewards that come with cyberattacks are increasing every day.
This is reflected in the demand for cybersecurity roles – with even entry-level cybersecurity analyst roles often earning more than $100,000/year.
But at the moment, There is an estimated current gap of 3.5 million unfilled cybersecurity roles.
Cybersecurity is a lucrative and in-demand career path that doesn’t look like it will go away anytime soon. But helpful tips for getting into this career are, however, somewhat rare compared to the well-worn paths to data science and software engineering.
I spent some time working in cybersecurity on my own startup, and I also helped launch a cybersecurity bootcamp. Based on my research, and some of the candid insights from the people I worked with, here’s some useful tips if you're considering your cybersecurity prospects.
Look for Entry-level or Mid-level Blue Team Roles
Screenshot of Indeed Search for Cyber Security Analyst (provided by author)
The distinction between blue team and red team roles is a critical inflection point for many cybersecurity careers.
You might be fascinated by tales of hackers tapping away and by movies about incredible hacking prodigies who get into the Pentagon’s systems. But the reality is that entry-level cybersecurity roles often involve getting experience on defense (“blue team”) and preventing attacks rather than starting them.
You’ll get started with an analyst role and work with companies to prevent attacks rather than simulating or trying them out most of the time.
Most “red team”/offensive roles that involve penetration testing are handled by agencies or external teams these days. Even companies that hire internal teams to do that work expect you to have played defense for some years before you’re part of an offensive team.
Certifications related to the offensive side such as the Certified Ethical Hacker (the CEH) are often given out with years of work experience as a prerequisite. You need a minimum of 2 years of security-related experience to even test for the CEH, for example.
If you have a military background, initiatives like this one by Microsoft will help get you structured for success in entry-level cybersecurity roles and will help transition you from military to civilian life.
Network within Associations
Local professional associations and meetups are a great way to get to know the cybersecurity community at large. Mark it as an essential step towards getting started and building both cybersecurity knowledge and a network.
This is a great way to develop your soft skills as well – a critical need in cybersecurity roles involves communicating with multiple teams.
The following article has a list of associations that are cybersecurity-related, as well as a section dedicated to associations that are driven to get more women into cybersecurity.
Certifications are Good, but Experience is Worth its Weight in Gold
There are a bunch of certifications, from CompTIA’s Security+ to others that will help signal your readiness for cybersecurity jobs. Some are more entry-level and require IT competencies such as the A+. But some will require you to have job experience in cybersecurity (such as the CISSP).
There’s a bit of a chicken and egg situation and you might wonder – how can you get job experience if you need job experience to get the job in the first place?
Adjacent job experience can often make a difference here. Many people transition into cybersecurity from IT roles, such as network administration, system administration, or being on helpdesk for IT, which is an entry-level role. You can gain experience here and transition over.
There are also programs tailored for veterans and people with law enforcement backgrounds to get into cybersecurity. Lastly there are many cybersecurity internships being offered to bridge this gap – though with the right backing, training, and the right experience, you can skip ahead to junior-level analyst roles.
Look for Security Operations Centers Analyst Roles
SOC analyst roles are a good way to break into the cybersecurity industry. Security operations centers need analysts to parse through different threats. This entry-level role pays $71k on average, and can be a good way to demonstrate your capabilities before moving on to more advanced roles.
You’ll need technical knowledge, but the depth of experience required here isn’t so deep. This marks it as a great way for people who are self-taught developers, familiar with SQL, Python, web applications and the terminal to move into a cybersecurity role and begin their career.
Like we talked about earlier, this is a defensive “blue team” role that will help you get started down the path to more advanced roles. Here’s a sample job description outlining the role.
As you can see from that job description, you’ll need familiarity with industry-specific tools such as a SEIM (Security information and event management tool) and SOAR (Security orchestration, automation and response tool). You'll also need experience with the command line and scripting, and knowledge of cybersecurity frameworks.
While this particular outline calls for 2 years+ of related experience in security operations, there are quite a few that don’t require too much entry-level experience.
SOC analyst roles are generally regarded as a good entry-level position for people looking to pivot and transition deeper into a cybersecurity career.
Practice Your Scripting Skills, Especially with Linux
Image from Wikimedia Commons
In order to be fully effective in cybersecurity, understanding how to code and systematically look through logs is essential.
With active, large corporate sites, there might be thousands or even tens of thousands of hits every minute. And sifting through and being able to identify threat actors requires some knowledge of programming to decipher it all.
If you’re looking to advance into cybersecurity, it’s good to know how to programmatically work and analyze the flood of data that comes with it.
This will involve getting comfortable with the terminal, working on Python and shell scripts, and other programming skills. You’ll want to think about deploying real-time algorithms that are able to sift through data accurately and reliably.
In general, you’ll want to be strong enough with Linux commands or other terminal commands to do the following:
View critical system information and status
Be able to detect running processes and programs and start/stop them
Install software and be able to update it securely (configuration of automatic installation may be required)
Connect into remote systems using tools such as SSH
Go through events logs and be able to systematically understand what is happening to a system
Set up events logs in such a way that you can be maximally efficient at responding to threats
View how the network is set up and make changes as needed, and make system changes as needed as well
Out of these skills, a couple of programming mainstays will help you a lot.
Knowledge of regular expressions, a way of finding patterns within large blocks of code, will quickly help you go through logs to find out what is happening. And BASH scripts are useful for interacting with the terminal in a more systematic way,
You can sharpen these skills by playing games or reading through materials. If you’re on a Mac or Linux computer, you’ll already have a head start with a Linux-like or Linux terminal wrapped up as a default app. Otherwise, you can practice with Microsoft Powershell.
There are also courses devoted to the Terminal, from offerings such as Colt Steele’s course on Udemy to Codecademy’s interactive Pro course devoted to the topic. Or if you prefer a more systematic approach that ties together these technical skills as well as the tools and compliance measures you need to consider, look at something like Springboard’s cybersecurity bootcamp.
Learn Commonly Used Cybersecurity Tools
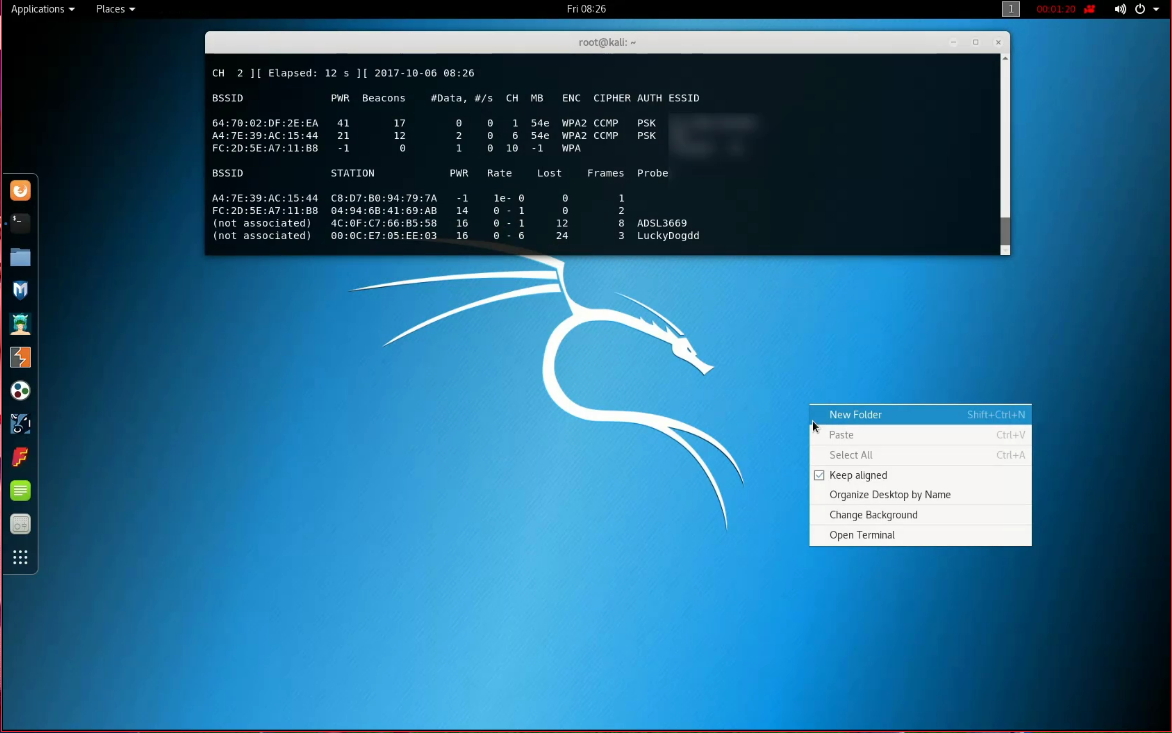
Image of Kali Linux from Wikimedia Commons
There are a suite of cybersecurity-specific tools, such as Kali Linux, that will be useful to any aspiring analysts. Playing around with them can give you a lot of practice and understanding of the modern cybersecurity stack.
Here are a few examples of tools you should be familiar with for the cybersecurity analyst level:
NMap is an open source tool that lets you easily map out different network ports, and allows you to do basic vulnerability scanning.
Wireshark lets you sniff packets of information from a network. You can use it to break down real-time data on a live network, giving you detailed information on the data passing within a network.
John The Ripper is a password cracker meant to detect when there are weak Unix passwords. This is an important check to make sure that users with admin privileges have secure accounts so that an external attacker cannot have access to system privileges they would need to escalate an attack.
Snort is open source software that allows you to detect network intrusion. It can do live traffic analysis and figure out if there’s malicious software on inbound requests, allowing you to more easily defend a network from malicious actors.
Metasploit allows for deeper analysis of the results from tools like NMap and Wireshark. While it’s used primarily as a penetration testing tool, you can use it to lay the foundation for a good network defense. It used to be open-source and totally free, until a company acquired the software. You can still use the free community edition to practice getting familiar with it, however.
Learn Commonly Used Compliance Frameworks
Cybersecurity is not just a technical endeavor. You have to understand different compliance frameworks and rigorously go through them.
Cybersecurity, after all, isn’t just about technical skills. It’s about standards and audits, as well as defining processes so that security can be effectively applied across organizations.
You’ll want to be familiar with some general compliance frameworks as well as industry-specific ones, especially for highly sensitive and regulated industries such as military or health work.
Here are just a few to consider:
CMMC, specifically for military contractors who want to deal with the US Department of Defense.
The OWASP Top Ten is a list of the top ten security risks for web applications that is openly published – a good structured way to think about cybersecurity risks.
HIPAA governs the data security practices in the healthcare industry. There are strict fines and consequences for deviating from those standards, which are set in US law.
GDPR is a set of data and cybersecurity laws passed in the European Union that are driving standards forward for how websites can collect and process data.
SOC-1 and SOC-2 audits are mostly focused on startups or other companies selling to large banks and other financial institutions. Specific rules and processes are checked in order to assure large financial institutions that they’re dealing with credible partners.
On this last point, it’s critical to keep up with evolving technical standards, tools, and compliance frameworks.
While it’s probably most worth keeping up on the news when it comes to new laws and new responses to attacks, a well-rounded cybersecurity interest in technical updates, compliance updates, and community updates is best to really craft a meaningful and long-lasting career in cybersecurity.
Resources that can help in this regard are newsletters such as Security Weekly, and the Sophos Naked Security site, as well as general news sites such as Hacker News.
Wrapping up
Having technical interests and some programming skills doesn’t just restrict you to careers in data science, web development, and IT. You can defend essential systems and data as a cybersecurity analyst, and transition into a lucrative and future-proof career in cybersecurity.
If you feel like you need help with 1:1 mentorship from industry experts and a curriculum built by hiring managers, Springboard has a cybersecurity bootcamp backed by a job guarantee that ensures you can leverage this tangible, useful advice towards a new career in cybersecurity.

