By Andrew Brown
What is the Microsoft Security, Compliance, and Identity Fundamentals?
The Microsoft Security, Compliance, and Identity Fundamentals Certification is an essential entry-level certification into Azure and Microsoft Security.
In recent years we've seen a significant shift in the work environment where companies allow employees to work from home.
The increase of IoT devices means we have more technology outside the office. The low cost of tablets and smartphones means we have more employees carrying around sensitive data. Companies are leveraging more cloud services, and employees can procure their software without the approval of a centralized IT department.
Our people, devices, and software are no longer contained within the boundaries of a single physical location. So we must change the way we think of cybersecurity by treating our primary security as being focused around Identity.
Microsoft's Active Directory is the industry standard for enterprise identity. With Microsoft's cloud variant Azure Active Directory, it is easy for a company of any size to have the best-in-class identity management and directory service and quickly implement a Zero-Trust model.
Overview of the Microsoft Security, Compliance, and Identity Fundamentals
The Azure Data Fundamentals covers the following:
- Zero-Trust Model, Security, Compliance Concepts
- Azure AD
- M365 and Azure Defender
- M365 Compliance Center
- Various Azure Security and Networking Services
How do you get the Microsoft Security, Compliance, and Identity Fundamentals certification?
You can get the certification by paying the exam fee and sitting for the exam at a test center partnered with Microsoft Azure.
Microsoft Azure is partnered with Pearson Vue and PSI Online who have a network of test centers around the world. They provide both in-person and online exams. If you have the opportunity, I recommend that you take the exam in-person.
Microsoft has a portal page on Pearsue Vue where you can register and book your exam.
That exam fee is $99 USD.
Can I simply watch the videos and pass the exam?
For a fundamental certification like the SC-900 you can pass by just watching the video content without exploring hands-on with the Azure services on your own.
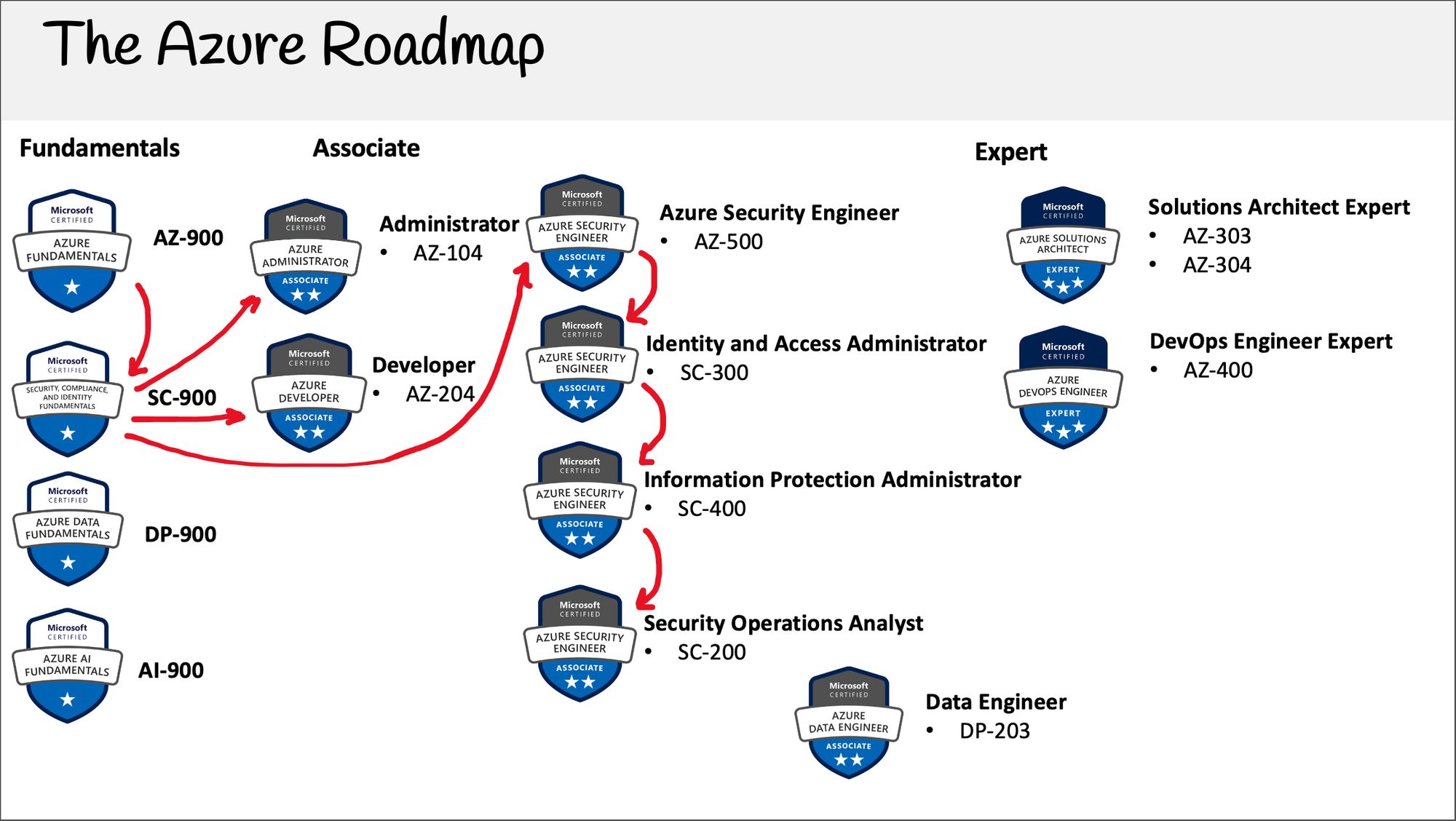
The SC-900 is the most lecture heavy fundamental certification by Microsoft and that is because it is laying the foundation for four possible Security Associate certifications.
Azure has a much higher frequency of updates than other cloud service providers. Sometimes there are new updates every month to a certification however, the SC-900 is not hands-on focused, so study courses are less prone to becoming stale.
- The exam has 40 to 60 questions with a timeline of 60 minutes.
- The exam contains many different question types.
- A passing grade is around 70%.
The Free Microsoft Security, Compliance, and Identity Fundamentals Video Course
Just like my other cloud certification courses published on freeCodeCamp, this course will remain free forever.
The course contains study strategies, lectures, follow-alongs, and cheatsheets, and it's designed to be a complete end-to-end course.
Head on over to freeCodeCamp's YouTube channel to start working through the full 3.5-hour course.
Here are the full contents of the course
Introduction
- What is the SC 900
- Exam Guide
Security Methodologies
- Zero Trust Model
- Zero Trust Principles
- Zero Trust Pillars
- Zero Trust Assessment Tool
- Follow Along Zero Trust Assessment Tool
- Shared Responsibility Model
- Defense In Depth
- CIA Triad
Security Concepts
- Common Threats
- Vulnerabilities
- Encryption
- Cyphers
- Cryptographic Keys
- Hashing and Salting
- Digital Signatures
- In Transit vs At Rest
- MFA
- SIEM
- SOAR
- XDR
- EDR
- CASB
- Security Posture
- CSPM
- JIT & JEP
- Ingress vs Egress
- Shadow It
- AIR
- Threat Modeling
- STRIDE
- Follow Along Microsoft Threat Modeling
- IDS IPS
- MITRE Attack Framework
- Follow Along Mitre Attack Framework
Privacy
- Microsoft Privacy Principles
- Microsoft Privacy
Identity
- Primary Security Perimeter
- Identity Providers
Azure AD
- Introduction to Azure AD
- Active Directory vs Azure AD
- App Registrations
- External Identities
- Service Principle
- Managed Identity
- Device Management
- MDM & MAM
- Windows Hello
- Azure AD Connect
- SSPR
- Password Protection
- Identity Management Best Practices
- Emergency Access Accounts
Azure AD Authentication
- Authentication Methods
- Microsoft Authenticator
- Follow Along Microsoft Authenticator
- Biometrics
- FIDO and Security Keys
- Open Authentication
- Passwordless Authentication
Azure AD Management
- Conditional Access
- Azure AD Roles
- RBAC
Azure AD Protection Governance
- Identity Governance
- HCM
- Identity Lifecycle
- Access Lifecycle
- Privilege Access Lifecycle
- Entitlement Management
- PIM
- Identity Protection
- Detection and Remediation
- Investigation
Azure NSG
- NSG Rules
- Default Security Rules
- Security Rules Logic
- NSG Combinations
- NSG CheatSheet
Azure Firewall
- Azure Firewall
Azure DDoS Protection
- Azure Ddos Protection
Azure Bastion
- Azure Bastion
Azure WAF
- Azure WAF
Encryption
- Encryption Overview
- Azure Disk Encryption
- TDE
- Key Vault
Azure Security Center
- Azure Security Benchmark
- Azuire Security Center
- Azure Security Benchmark Detailed
Azure Defender
- Azure Defender
Azure Sentinel
- Azure Sentinel
- Data Sources
- Workbooks
- Sentinel Features
- Sentinel Pricing
M365 Defender
- M365
- M365 Defender
- Secure Score
- Defender for Endpoint
- Security Reports
- Defender for Indentity
- Defender for Office 365
- MCAS
Microsoft Endpoint Manager
- Microsoft Endpoint Manager
Compliance
- Regulatory Compliance
- M365 Compliance Center
- Azure Trust Center
- Compliance Manager
- Follow Along Compliance Manager
- Compliance Programs
Protection and Governance
- MIP
- Know Protect Prevent
- GIP
- Sensitive Information Types
- Trainable Classifiers
- Content Explorer
- Activity Explorer
- Sensitivity Labels
- Label Policies
- Retention Labels and Policies
- Records Management
- DLP
Risk Capabilities
- Insider Risk Management
- Communication Compliance
- Information Barriers
- Privilege Access Management
- Customer Lockbox
- eDiscovery
- Core eDiscovery Workflow
- Content Search and Holds
- Advanced eDiscovery Workflow
- M365 Audit
Azure Security Concepts
- Resource Locks
- Resource Tags
- Azure Blueprints
- Azure Policy
- Cloud Adoption Framework
- Well Architected Framework
- Microsoft Security Best Practices
- Follow Along Microsoft Security Best Practices
- SAS
- CORS
- SDL
